In a controlled demonstration filmed for Veritasium, cybersecurity researchers extracted $10,000 from YouTuber Marques Brownlee’s locked iPhone. They did so without unlocking the device, using biometric authentication, or seeing any alert appearing on screen (except for the successful transaction notification). The Visa card vulnerability behind this feat is not new and was first disclosed to Apple and Visa back in 2020. Now, many years later… it remains worryingly unpatched.
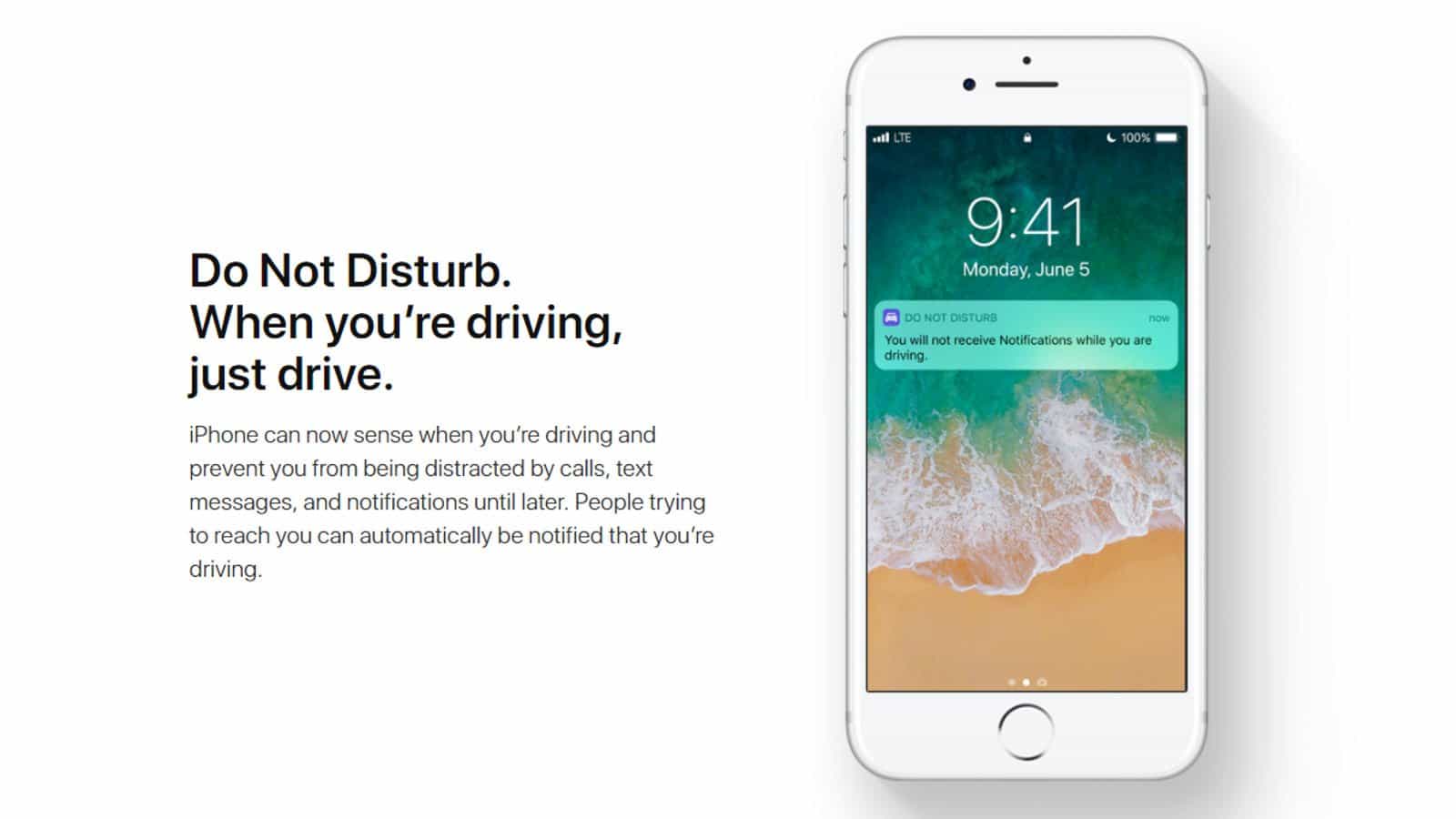
In the simplest sense, the exploit targets iOS’ Express Transit functionality – a convenience feature Apple introduced in 2019 allowing iPhone users to tap through public transport barriers without unlocking their devices. For commuters navigating turnstiles at speed, Express Transit removes the friction of Face ID or Touch ID authentication; with the Near Field Communication (NFC) chip simply processing the payment as a tap-and-go transaction. It is a thoughtful quality-of-life feature designed to keep queues moving and commuters unbothered. The problem, however, lies not with the feature, but with how Visa processes the transactions it enables.
How the Visa Card Vulnerability Works
The attack – developed by researchers Andreea-Ina Radu and Dr Tom Chothia at the University of Birmingham, alongside Dr Ioana Boureanu, Dr Christopher J.P. Newton, and Professor Liqun Chen at the University of Surrey – functions as an active man-in-the-middle relay. When an iPhone approaches a legitimate transport terminal, the terminal broadcasts a specific sequence of non-standard bytes (dubbed “magic bytes” by the research team) before the standard NFC wake-up command. These bytes tell Apple Pay the transaction is happening with a transit reader; in so doing, the device bypasses its usual authentication requirements.
The researchers discovered they could replicate these magic bytes using a Proxmark Radio-Frequency Identification (RFID) device connected to a laptop, effectively tricking any iPhone into believing it was communicating with a transport gate. A second device – an NFC-enabled Android phone acting as a card emulator – then relays the transaction data to a legitimate payment terminal elsewhere. The attack is sophisticated and actually goes further still by modifying specific flags in the Europay, Mastercard, and Visa (EMV) protocol messages (namely the Terminal Transaction Qualifiers and Card Transaction Qualifiers), which allowed the researchers to bypass both the contactless payment limit and the on-device authentication check. The payment terminal, in turn, receives confirmation consumer verification was performed on the device… even though it was not. The result is a transaction of virtually any amount, processed from a locked iPhone, with the payment terminal believing everything was properly authorised. The upside is how this only affects Visa cardholders.
Several Years and Counting
The timeline is perhaps the most troubling dimension of this story. The researchers first disclosed their findings to Apple in October 2020 and to Visa in May 2021. The research was subsequently presented at the 2022 Institute of Electrical and Electronics Engineers (IEEE) Symposium on Security and Privacy – one of the most prestigious venues in the field. It generated significant media coverage at the time, with many popular outlets and news organisations detailing the flaw. Strangely, neither company saw fit to act and remedy the situation.
Veritasium’s latest video – in which the researchers demonstrate the full attack chain – has once again reignited public attention. Yet the underlying reality remains unchanged: neither Apple nor Visa has deployed a fix. As lead researcher Dr Andreea Radu noted at the time of the original disclosure, when two industry parties each bear partial blame, and neither proves willing to accept responsibility; it is the users who are left indefinitely vulnerable.

The Fault in Visa’s Stars
Attributing blame requires understanding the payment processing hierarchy. Apple Pay, Samsung Pay, and Google Pay are all facilitators of payments, not arbiters of their veracity. Their sole function is to reliably pass transaction data to the card network. They are not banks, thus they do not (and should not) decide whether a transaction looks suspicious, and they are designed to work predictably and reliably regardless of currency, location, or fare structure. The card network – in this case Visa – is the entity responsible for validating the transaction against its own security protocols before passing the decision to the issuing bank.
Mastercard, in comparison, performs this validation correctly and the contrast reveals exactly where Visa fails. The over-the-limit attack succeeds against Visa for one central reason: when the attacker flips the bit in the Card Transaction Qualifiers (CTQ) telling the terminal “on-device authentication has been performed”, Visa does not cryptographically authenticate that field – nor does it cross-check it against the Issuer Application Data (IAD), which contains an independent record (in the Card Verification Results field) of whether Consumer Device Cardholder Verification Method (CDCVM) actually occurred. During the original disclosure process, Visa confirmed to the researchers the relevant data is present in the Application Cryptogram; the company simply does not validate it – whereas Mastercard does. The researchers proved this formally using the Tamarin verification tool: a Mastercard transaction cannot be approved at high value without genuine on-device authentication.
There is a secondary defence, too. Mastercard’s protocol cryptographically authenticates the Merchant Category Code (MCC), meaning a relayed transaction sent to a non-transit reader (a jewellery store, an electronics shop, etc) is detected and rejected because the MCC does not match what is signed in the transaction data. It is worth noting this defence is not absolute – the researchers found Mastercard relays to other transit terminals are still possible – but the practical attack surface is dramatically reduced. American Express, according to reporting on the Veritasium demonstration, is also unaffected by the attack, though the underlying research did not test AMEX directly, and the technical reason for its immunity has not been formally established.
Simply put, Visa chooses to not cryptographically authenticate a field the company knows can be exploited. Therefore, the flaw is not really a question of missing encryption or absent hardware capability; it is more so a verification gap in Visa’s own backend logic. Mastercard solved this exact problem, yet Visa, weirdly, chooses not to.
On the touch point of this exploit being one only affecting Apple’s iPhone, it is worth noting how Samsung Pay takes a different approach at the device level – authorising only zero-value transactions in transit mode, with the actual fare settled later through the transit system. This is effective, though it comes with trade-offs; like how fixed-fare transit systems requiring upfront charges are not supported. Apple could theoretically implement a similar restriction, yet doing so would break Express Transit for several transit networks worldwide. The more appropriate long-term solution requiring no compromise on device-level functionality, is simply for Visa to implement the same backend verification Mastercard already uses.

Visa’s Defence: Impractical at Scale
Visa’s official position, reiterated to Veritasium in 2026, is straightforward: the company does not believe the exploit is likely in a real-world setting. The attack requires physical proximity to (or possession of) the victim’s iPhone, specialised hardware, a rooted Android phone, and technical knowledge of EMV protocol manipulation. Visa further notes cardholders are covered by its ‘Zero Liability Policy’, allowing for any fraudulent transaction to be disputed and refunded. Anyone who has ever tried getting a refund from a bank for fraudulent activity will know how tedious and time consuming this process can be, and it is rather telling how Visa would rather put users through inconvenience than simply fixing the known security gap.
With that said, the company’s position is worth examining over outright dismissing. For a start, the hardware requirements are not trivial. Nefarious parties would require a Proxmark device, rooted Android phone, and laptop running custom relay software – all of which represent a higher barrier to entry than most opportunistic theft. Scaled deployment across hundreds of victims simultaneously is, indeed, impractical with current methods.
Even so, this defence has clear structural weaknesses. The existence of a known and, in this case, reproducible vulnerability in a payment network processing billions of transactions annually; cannot simply be mitigated by the argument of it being ‘difficult to exploit at scale’. Mastercard clearly agrees given how they have implemented protections against exactly this class of attack. Moreover, the equipment required is commercially available (the Proxmark, for instance, is an open-source RFID research tool), and the researchers’ methodology was published in full at a major academic conference. It also stands to reason how the barrier to replication lowers every year. Arguing a vulnerability is tolerable because exploitation is currently inconvenient is not a security posture… it is more akin to something of a d-day countdown.
What You Should Do Right Now
For anyone who regards the security of their financial data as a priority, the recommended course of action is clear and immediate: do not use a Visa card for Express Transit on an iPhone until either Apple or Visa deploys a fix.
To disable Express Transit for Visa on an iPhone, navigate to Settings, then Wallet and Apple Pay, then Express Transit Card, and select None; or assign either a Mastercard or American Express card to the feature instead. Both alternatives are, as of the publication of this article, immune to this specific Visa card vulnerability.
If you have already lost or had an iPhone stolen, activate Lost Mode immediately through Find My and contact your bank to block the linked Visa card. Visa’s Zero Liability Policy should cover unauthorised transactions, although the burden of dispute falls on the cardholder, which, to be blunt, is an inconvenience no one should have to endure for a flaw the card network could resolve.
The Longer Wait
The researchers behind this disclosure – who, it bears repeating, presented their findings to Apple and Visa in 2020 and 2021, respectively – offered a measured assessment at the time of the original publication. Dr Boureanu observed users should not have to trade security for usability. Half a decade later, that observation has aged into an indictment. Visa processed over 257 billion transactions in fiscal year 2025 alone; and the infrastructure to validate an MCC code exists and is already operational on competing networks. The Visa card vulnerability at the heart of this story is not a feat of novel exploitation, but it is a very clear failure of corporate will.
Owner, founder and editor-in-chief at Vamers, Hans has a vested interest in geek culture and the interactive entertainment industry. With a Masters degree in Communications and Ludology, he is well read and versed in matters relating to video games and communication media, among many other topics of interest.